AI Pathfinder | Issue #61 | Enterprise AI Intelligence for Operators
The arms race in AI cybersecurity just shifted. For the past year, the biggest complaint from enterprise security teams has been that frontier AI models are too restricted to be useful for actual defense. If you ask an AI to write a proof-of-concept (PoC) exploit to test your own network, it refuses.
OpenAI just changed that. They are rolling out GPT-5.5-Cyber and the Trusted Access for Cyber (TAC) framework — handing the keys to verified defenders while keeping the guardrails up for everyone else. Think of it as OpenAI’s direct answer to Anthropic’s restricted Mythos Preview model: instead of locking capability away, they are tiering access by verified identity.
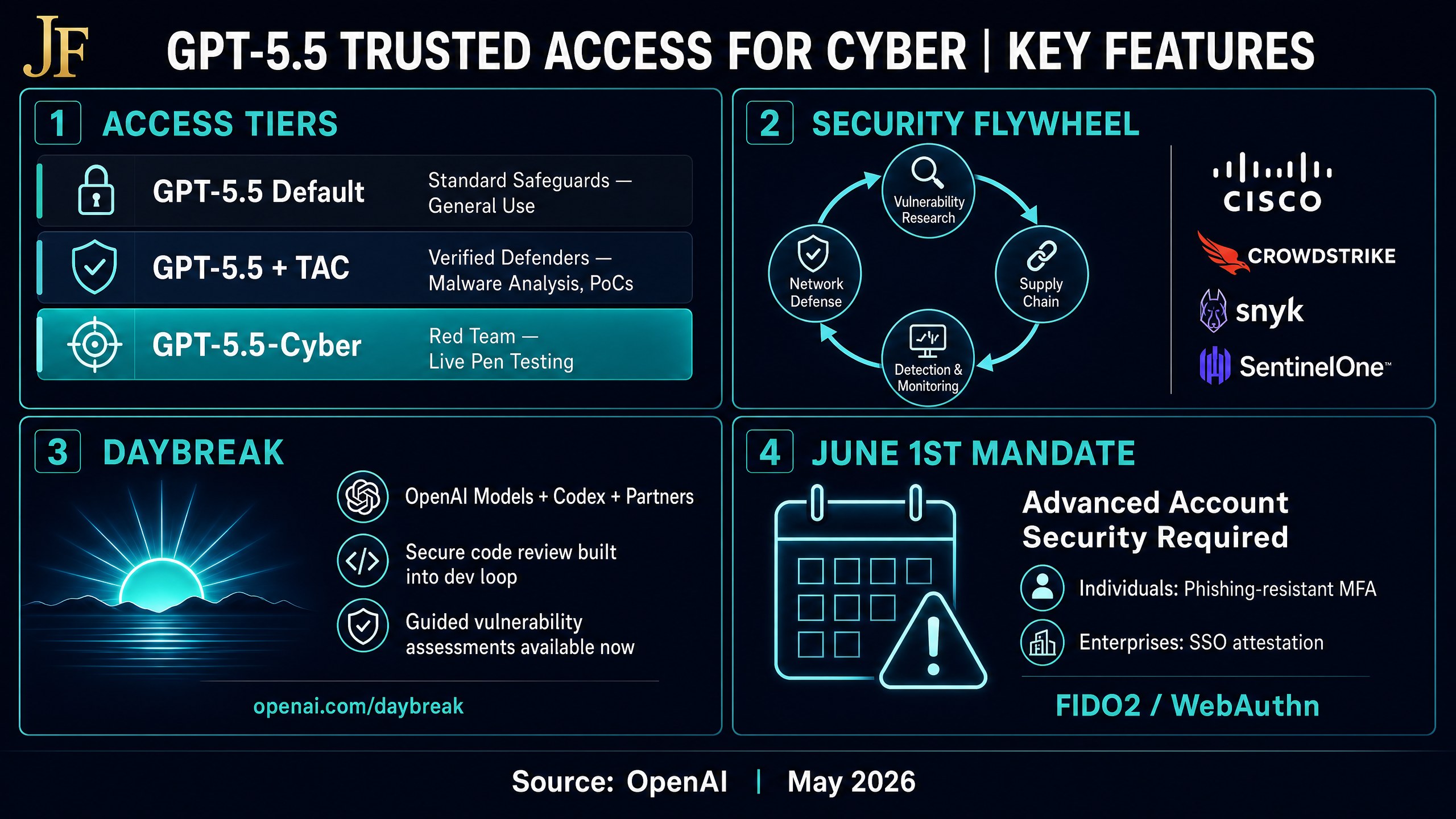
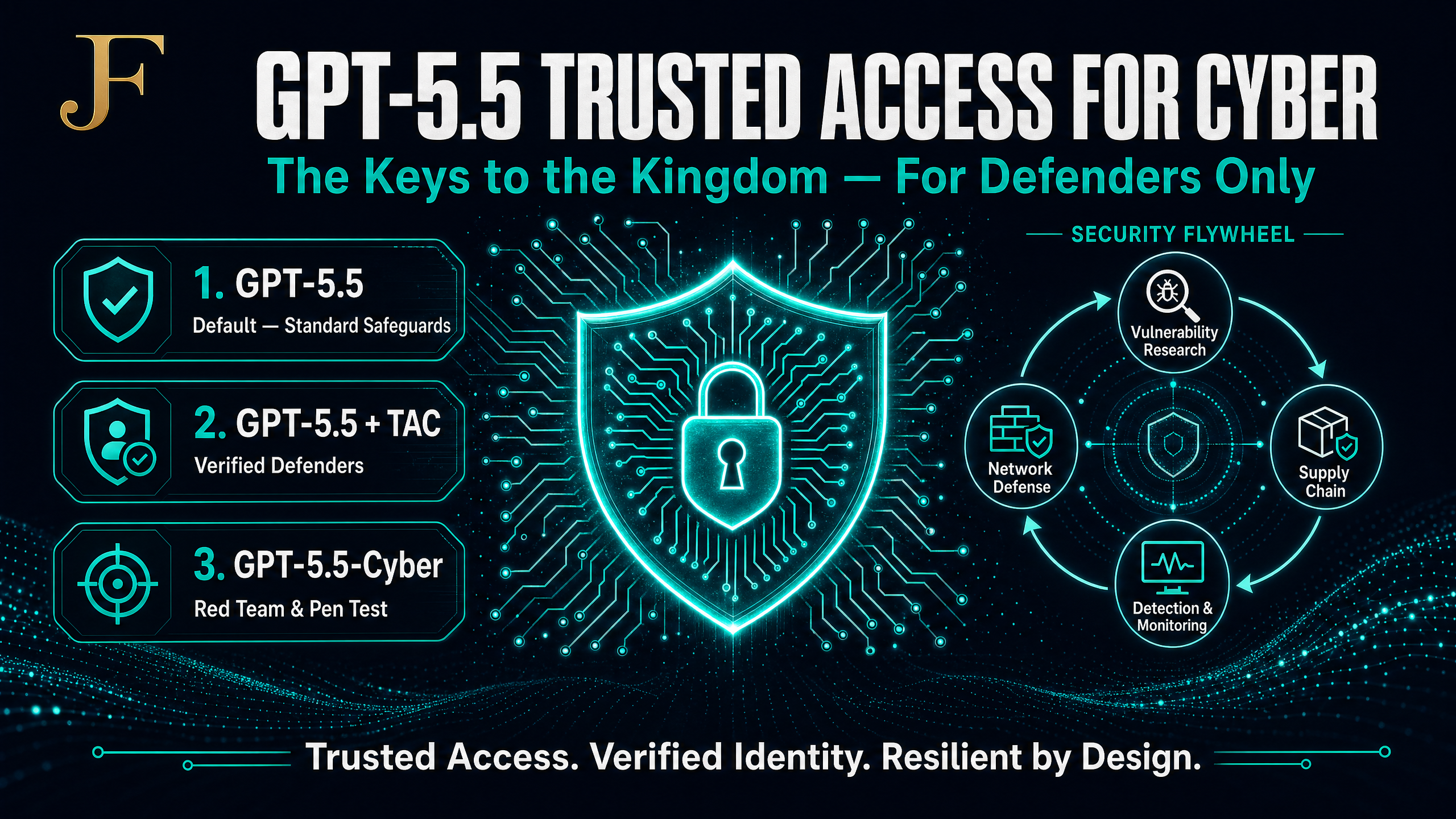
The Three Tiers of GPT-5.5 Cyber Access
OpenAI is segmenting model capabilities based on verified identity and intent. Here is how the new GPT-5.5 cybersecurity access model breaks down:
- GPT-5.5 (Default): Standard safeguards. Refuses exploit generation and malicious activity. Built for general-purpose knowledge work.
- GPT-5.5 with TAC (Trusted Access for Cyber): Lowered refusals for verified defenders. Allows vulnerability triage, malware analysis, binary reverse engineering, and defensive PoCs.
- GPT-5.5-Cyber (Preview): The most permissive tier. Designed for specialized workflows like authorized red teaming, live-target penetration testing, and controlled exploit validation.
The difference is stark. Ask the default model to create a PoC for a CVE and it flags the chat. Ask GPT-5.5 with TAC and it writes the exploit payloads, documents the setup in a README, and offers to add a patched variant for comparison.
The OpenAI “Security Flywheel” Ecosystem
OpenAI is not just releasing a model — they are embedding it into the entire cybersecurity supply chain. They are partnering with major security vendors to create a security flywheel where vulnerability discovery, detection, and enforcement improve simultaneously across the industry.
- Network & Security (Cisco, Palo Alto Networks, CrowdStrike): Deploying WAF rules and edge mitigations while fixes roll out.
- Vulnerability & Patching (Intel, Tenable): Tracing root causes, reviewing patches, and building safe reproduction harnesses.
- Detection & Monitoring (SentinelOne, Okta): Connecting telemetry signals, drafting detections, and accelerating incident response.
- Supply Chain Security (Snyk, Semgrep): Preventing vulnerable dependencies from reaching production builds.
OpenAI Daybreak: Resilient by Design
Alongside TAC, OpenAI announced Daybreak — their vision for a new era of cyber defense. The premise: the next era of cybersecurity should be built into software from the beginning. It is not just about finding and patching vulnerabilities; it is about making software resilient by design.
Daybreak combines the intelligence of OpenAI models, the extensibility of Codex as an agentic harness, and their security partners. It allows defenders to bring secure code review, threat modeling, patch validation, dependency risk analysis, detection, and remediation guidance directly into the everyday development loop — shifting security left before vulnerabilities ever reach production.
OpenAI is currently offering companies a guided vulnerability assessment. If you want to see how this works on your own codebase, fill out the form on the Daybreak site.
The Phishing-Resistant MFA Mandate (June 1, 2026)
There is a catch. To access the most permissive models, you need to prove your identity is secure. Beginning June 1, 2026, individual members accessing GPT-5.5-Cyber via TAC must enable Advanced Account Security (phishing-resistant MFA). Enterprises can attest that they have phishing-resistant authentication at the SSO level.
This is a significant push for enterprise identity hygiene — OpenAI is directly tying advanced AI capabilities to zero-trust security principles. If your organization has not yet adopted FIDO2/WebAuthn, this deadline is your forcing function.
Your AI Cybersecurity Action Plan (3 Steps)
Here is what security and IT leaders need to act on this week:
- Audit your identity stack: Ensure your SSO supports phishing-resistant MFA (FIDO2/WebAuthn) so your team qualifies for TAC before the June 1st deadline.
- Apply for TAC: Get your SOC, threat hunting, and vulnerability management teams verified through your OpenAI representative.
- Integrate Codex Security: For development teams, start using the Codex Security plugin to shift threat modeling left and catch vulnerabilities before they merge into production.
Frequently Asked Questions
What is OpenAI Trusted Access for Cyber (TAC)?
TAC is an identity and trust-based framework by OpenAI that gives verified cybersecurity defenders access to less-restricted versions of GPT-5.5. It enables authorized defensive workflows — like malware analysis and PoC generation — without triggering standard safety refusals.
How does GPT-5.5-Cyber differ from the default GPT-5.5 model?
While the default model blocks exploit generation, GPT-5.5-Cyber is highly permissive for verified teams, allowing live-target penetration testing, automated red-teaming, and exploit validation in controlled environments.
Who qualifies for GPT-5.5 Trusted Access for Cyber?
Verified defenders, security researchers, and enterprise security teams — including SOC analysts, detection engineers, and penetration testers — who complete identity verification and meet strict account security requirements.
What is the June 1, 2026 security mandate for TAC?
By June 1, 2026, anyone accessing the most permissive cyber models via TAC must have Advanced Account Security (phishing-resistant MFA) enabled, or their organization must attest to having it at the SSO level.
What is OpenAI Daybreak?
Daybreak is OpenAI’s vision for building cyber defense into software from the start. It combines OpenAI models, Codex, and security partners to help defenders reason across codebases, identify vulnerabilities, and validate fixes faster — making software resilient by design rather than by patch.
How does OpenAI’s Security Flywheel impact enterprise cybersecurity?
By partnering with Cisco, CrowdStrike, Snyk, SentinelOne, and others, OpenAI is enabling a security flywheel where AI simultaneously accelerates vulnerability discovery, patch deployment, and network defense across the enterprise security ecosystem.
About Jason Fleagle
Jason Fleagle is the Head of AI for Netsync and an AI and Growth Consultant working with global brands to help with their successful AI adoption and management. He helps humanize data — so every growth decision an organization makes is rooted in clarity and confidence. Jason has helped lead the development and delivery of over 500 AI projects and tools, and frequently conducts training workshops to help companies understand and adopt AI.
If you need a team of AI experts to help your organization deploy secure AI workflows at scale, let’s talk with our team at NetSync.